FAQ¶
Hardware Compatibility¶
Supported Hardware¶
NLC is designed to run on a wide range of hardware, with the following requirements:
- Operating System: 64-bit
- CPU Architecture: 64-bit
- Note: NLC can be compiled for 32-bit systems, but 32-bit is not officially supported.
- Not Supported - Apple devices:
- This is due to high cost and Apple's restrictive platform policies.
Developer Test Bed¶
The following devices make up the author’s primary development and testing environment:
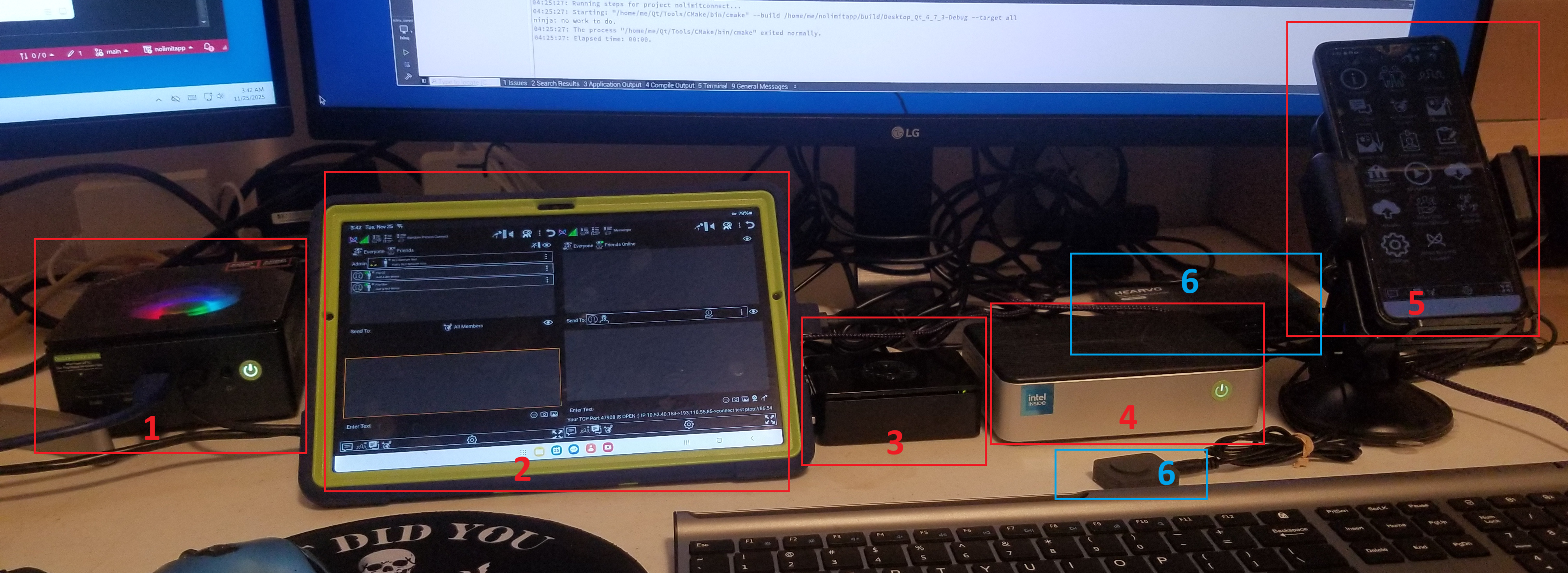
Devices:
- GMKtek K11 — Windows 11
- Galaxy Tab A8 — Android 14
- Raspberry Pi 5 — Raspberry Pi OS
- GMKtek G9 — Ubuntu 24.04
- Galaxy Flip G5 — Android 15
- Steetek KVM Switch — Shares keyboard/mouse/monitor between: Raspberry Pi 5 and GMKtek G9
Recommended Hardware for a NLC Network¶
To run NLC as a private network host, the following options are recommended:
-
An old 64-bit Android phone
-- No cellular service required
-- Low-power and suitable for always-on use -
Raspberry Pi 5
-- Cost-effective
-- Low energy usage
-- Ideal for 24/7 operation -
Any machine capable of running Linux
-- Desktops, laptops, mini PCs, etc.
Do I Need Dedicated Hardware to Host a NLC Network?¶
No. Hosting a private NLC network does not require specialized or dedicated hardware.
There are only two essential requirements for any type of NLC hosting:
- An active NoLimitConnect application instance
- An open network port
— Refer to the Connectivity section for detailed guidance.
With these basics in place, you can host a private network on virtually any compatible device.
How do I setup my own NLC Network¶
➡️ How To Setup A NLC Network Host
Why We Encourage Network Hosting¶
NLC is designed with a strong focus on privacy and freedom of expression. While the platform operates legally and transparently, history has shown that services promoting open communication can still face external pressures or attempts at deplatforming.
By enabling users to host their own networks, we eliminate reliance on any single organization or centralized service. This decentralized model ensures that:
- No single point of failure exists — individual networks remain operational even if others are targeted.
- Users maintain control over their data, uptime, and community policies.
- Censorship resistance is strengthened, as there is no central entity that can be taken down to silence the platform.
Encouraging distributed hosting empowers the community and protects the long-term resilience of NLC.
Encryption, Public and Privete Network Keys¶
Permission Levels¶
Permission to each plugin depends on permission level assigned to the plugin and permission level assigned to user